Identify stages in the cyberattack lifecycle and firewall mitigations that can prevent attacks. Palo Alto PCNSA Study Guide v10 The...
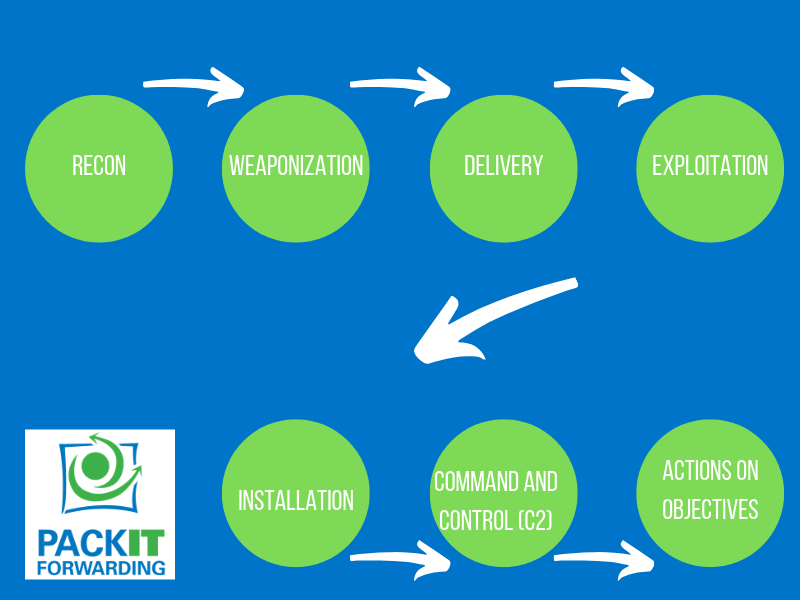
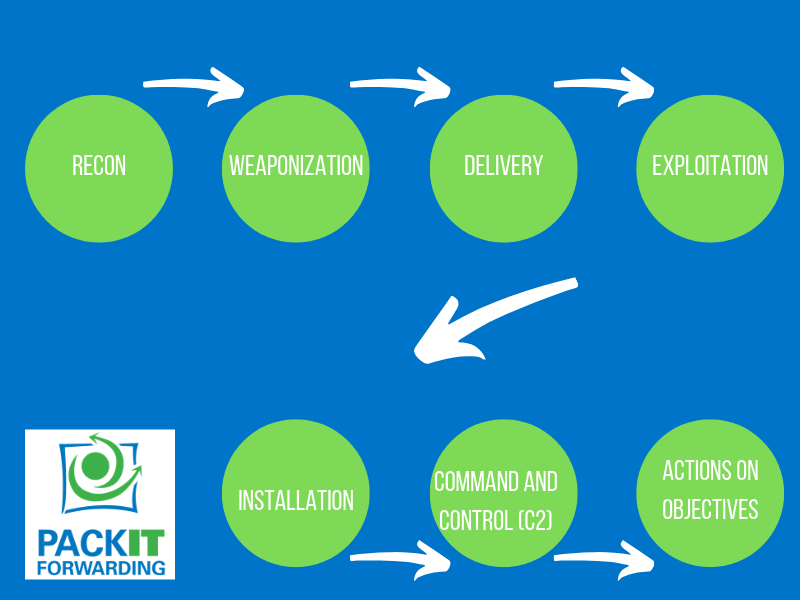
Identify stages in the cyberattack lifecycle and firewall mitigations that can prevent attacks. Palo Alto PCNSA Study Guide v10 The...

Given a network design scenario, apply the Zero Trust security model and describe how it relates to traffic moving through...

Identify the components and operation of Single-Pass ParallelProcessing architecture. Palo Alto PCNSA Study Guide v10 Single-Pass Parallel Processing The Palo...

Identify the components of the Palo Alto Networks Cybersecurity Portfolio. Palo Alto PCNSA Study Guide v10 Strata Strata consist of...