Given a scenario, prepare a toolkit and use appropriate forensics tools during an investigation.
CompTIA Cybersecurity Analyst (CySA+) Certification Exam Objectives Version 3.0
Being prepared before an event is a crucial part of being a security analyst. Developing a forensics toolkit is key in this preparedness.
Digital Forensics Workstation
The workstation for an investigation should be dedicated and
- Must have network connectivity.
- Must support hardware based drive duplication.
- Must support remote and network drive duplication.
- Must support duplication and analysis of common file systems.
- Must be able to validate image and file integrity.
- Must be able to identify dates and times files were modified, accessed and created
- Must be able to create file system activity timelines.
- Must be able to identify deleted files.
- Must be able to analyze drive space, both allocated and unallocated
- Must allow direct association of disk images and evidence to a case.
- Must allow the investigator to associate notes to cases and evidence.
- Must support removable media for storage
- Evidence must be admissible in a court of law.
Other Required Tools
- Write Blockers: Tool that does not allow a protected drive to be changed. It must not prevent obtaining information from or about the drive. The tool won’t protect other drives.
- Cables: A variety of cables for connecting to storage should be in the kit including USB, SATA
and FireWire along with power cables for drives. - Drive Adapters: Adapters to support
microSATA , SATA blade type SSD, SATA LIF and IDE - Wiped Removable Media: Media of various types ready to be used and any adapters to use them.
- Cameras: Most commonly a Digital SLR camera with at least 12-megapixel capability is used for evidence collection.
- Crime Tape: You must protect the physical scene and keep it from being contaminated.
- Tamper-Proof Seals: You must be able to securely store evidence with tamper-proof seals to maintain the chain of custody.
- Documentation and Forms: Forms should be pre-printed for ease of use during the investigation. Many can be found at the US Department of Justice.
- Chain of Custody Form: Keeps a list of who has handled the evidence, when they did and in which order they handled the evidence.
- Incident Response Plan: Details the processes and steps for responding to an incident.
- Step 1 – Detect: Detect the security incident.
- Step 2 – Respond: Appropriate response based on the type of incident. Responses and response times should be established ahead of time.
- Step 3 – Report: Report the incident based on the seriousness of the incident and previously defined procedures.
- Step 4 – Recover: Bring resources back to full capabilities while maintaining evidence.
- Step 5 – Remediate: Patch any vulnerabilities exploited and fix any other weaknesses found.
- Step 6 – Review: Review the lessons that can be learned from the incident and the response.
- Incident Form: Used to fully describe the incident in detail. Example templates can be downloaded from SANS.
- Call List or Escalation List: Contact information for those that may need to be alerted during an investigation and when they should be alerted.
Forensic Investigation Suite
It is important to be familiar with tools that are commonly using in a digital investigation.
- Imaging Utilities: Digital copies of storage must be made for backup and analysis. Two copies should be made, one for evidence and one for analysis. The Linux tool dd is one example of a bit by bit imaging tool.
- Analysis Utilities: Tools needed to analyze the copy of data created by the Imaging Utilities. An example of an open source tool is Autopsy.
- Chain of Custody: Hard copies must be maintained but tools can be used to automate the chain of custody.
- Hashing Utilities: Tools to verify information using either MD5 or SHA hashes. There are many open source tools to compute these hashes.
- OS and Process Analysis: Tools to analyze OS processes.
- Mobile Device Forensics: Tools to acquire information from mobile devices (tablets and phones).
- Password Crackers: Tools to crack password hashes such as JackTheRipper may be needed to analyze data.
- Cryptography Tools: Can attempt to decrypt data encrypted by common tools like BitLocker.
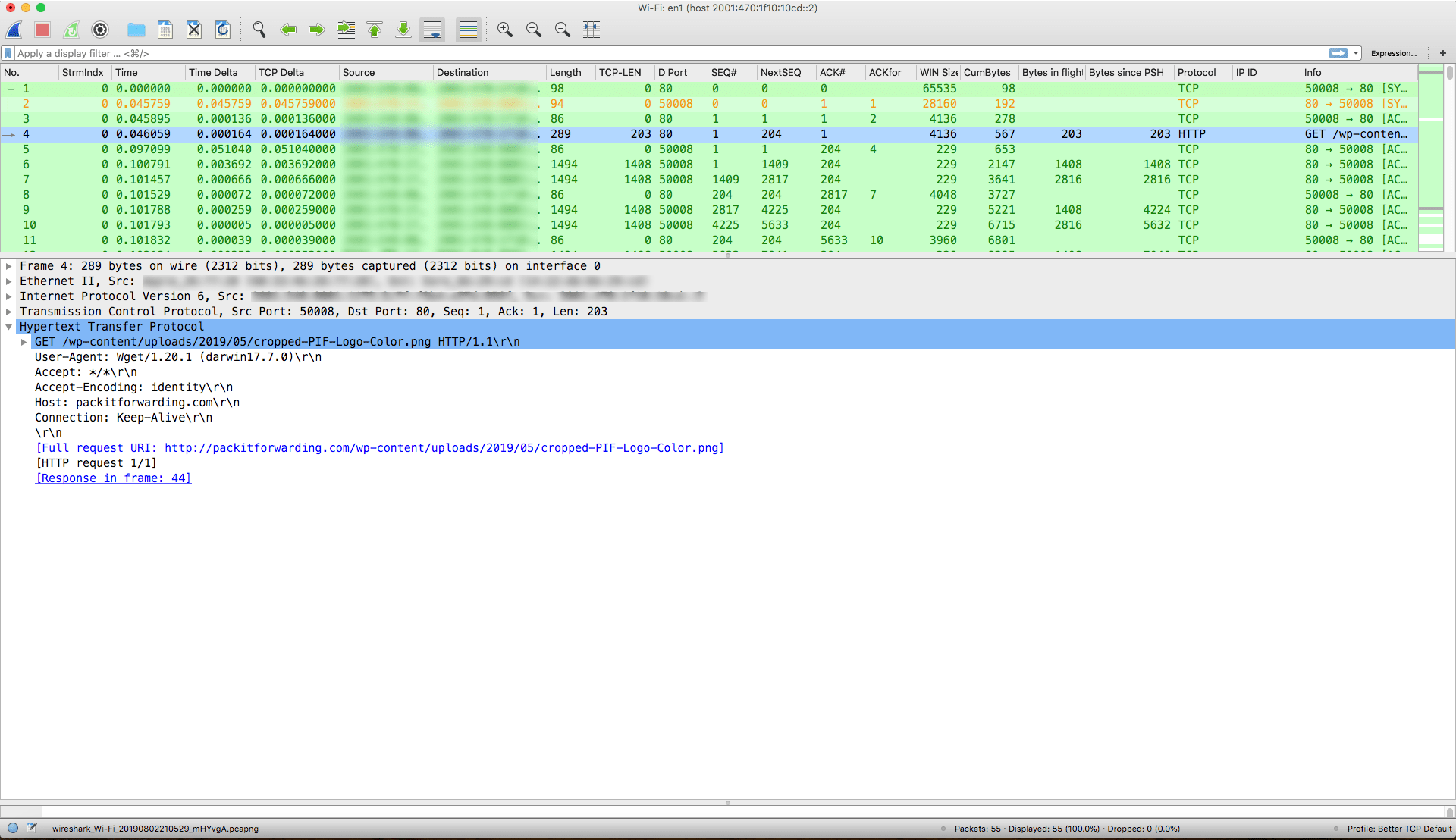
- Log Viewers: Tools to be able to read system logs easily.




1 thought on “CompTIA CySA+ Objective 3.2”