Identify these key elements in an intrusion from a given PCAP file : Source address, Destination address, Source port, Destination...
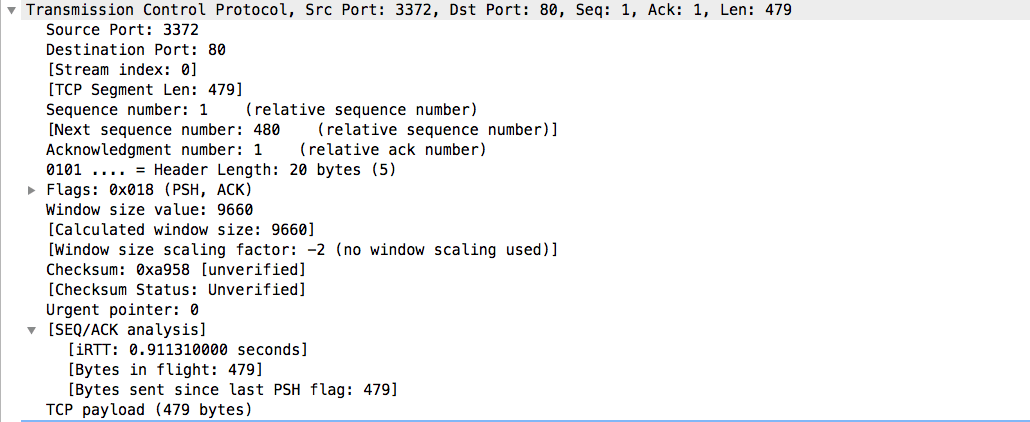
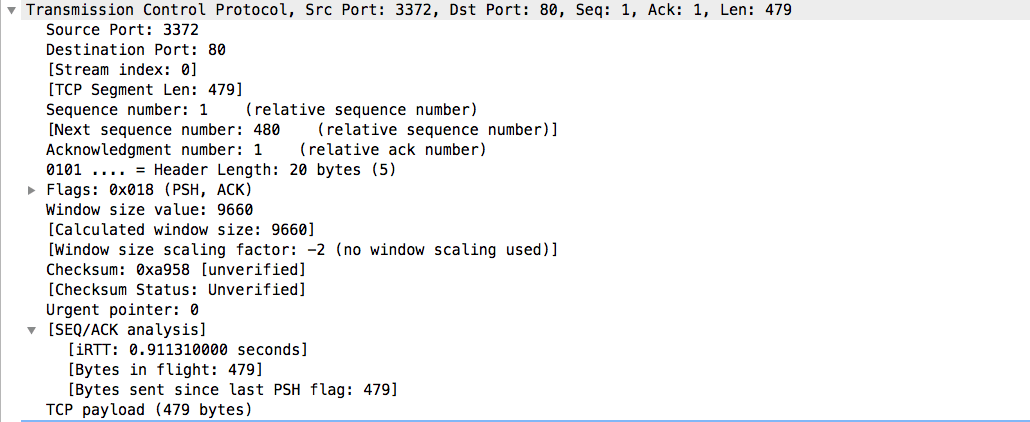
Identify these key elements in an intrusion from a given PCAP file : Source address, Destination address, Source port, Destination...