Given a network diagram, create the appropriate security zones. Palo Alto Networks PCNSA Study Guide v10 Palo Alto firewalls use...


Given a network diagram, create the appropriate security zones. Palo Alto Networks PCNSA Study Guide v10 Palo Alto firewalls use...

Configure internal and external services for account administration. Palo Alto Networks Study Guide v10 Administrative Role Types Role Based: These...

Identify and configure firewall management interfaces. Palo Alto PCNSA Study Guide v10 Management Access Web Interface CLI Panorama XML API...
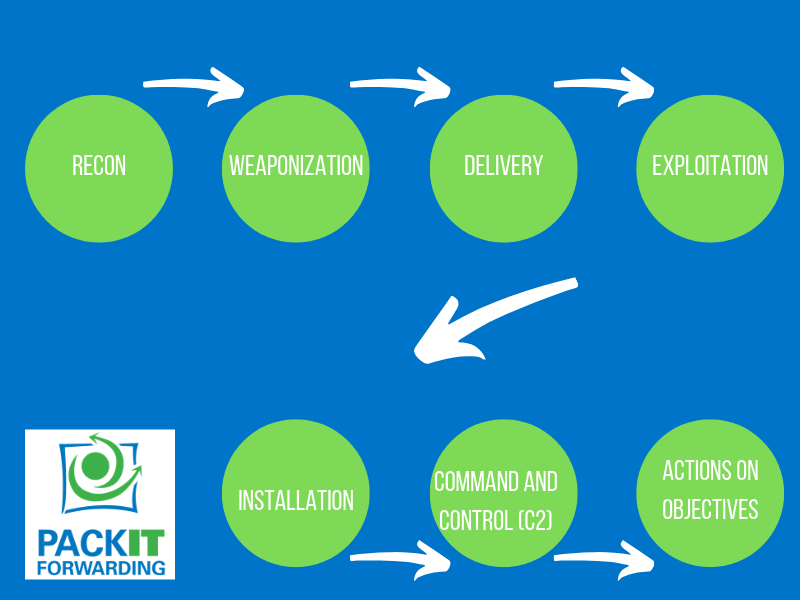
Identify stages in the cyberattack lifecycle and firewall mitigations that can prevent attacks. Palo Alto PCNSA Study Guide v10 The...