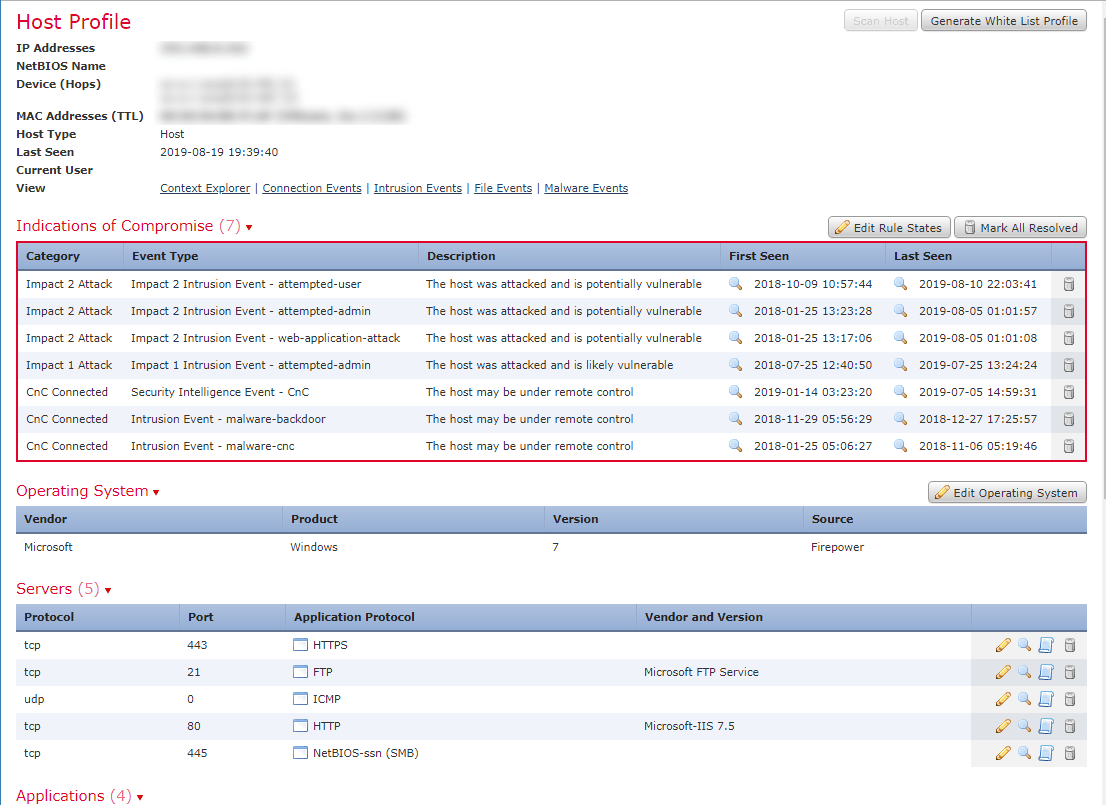
Identify potentially compromised hosts within the network based on a threat analysis report containing malicious IP address or domains
Implementing Cisco Cybersecurity Operations (210-255)
A threat analysis report helps an analyst by providing a list of all of the IPs or domains that a potentially compromised host has been communicating with. This information can help determine how the host was compromised and if data has been exfiltrated.
Reports from places like ThreatGrid about what a piece of malware does when executed are also useful. These can help an analyst know what kind of traffic to look for. A security analyst should be familiar with what a ThreatGrid report looks like and what information it contains.